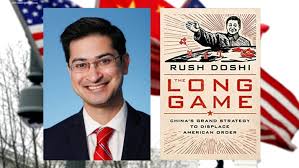
The Long Game; China’s Grand Strategy to Displace American Order, Rush Doshi, 2021
<> <> <> <> <> 
<> <> <> <> <> 
László Ladányi was a Hungarian Jesuit who lived in China from 1936 until his expulsion by the Communists in 1949. He moved to Hong Kong where he published China News Analysis from 1953 til 1982 when he retired to write books. China News Analysis was the only English language coverage of events from a closed China and based on published speeches and other high level official sources. He covered Mao’s paranoid machinations from the Great Leap Forward where Ladányi predicted 50 million Chinese deaths from starvation to the Cultural Revolution.
Rush Doshi adopted much of the research methodology of Ladányi in preparing this book which is a study of Chinese foreign policy (political, economic and military) from Deng Xiaoping to the present. Doshi notes that China inherited its nationalism from Sun Yat-sen and the Chinese century of humiliation at the hands of the west and the desire to return China to its historic role as the Central Kingdom surrounded by tribute bearing smaller states, and its political structure, the Chinese Communist CCP from Lenin.
<> <> <> <> <> 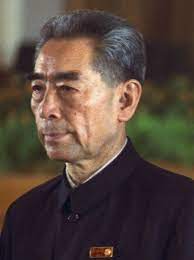
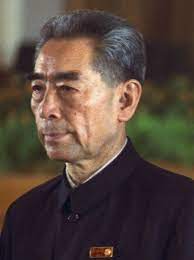
<> <> <> <> <> Zhou Enlai
In 1973 Chinese Premier Zhou Enlai visited Washington in preparation for Nixon’s visit to China. Zhou asked a young American member of the delegation “Do you think China will ever become an aggressive or expansionist power?” The American answered “No.” and Zhou said “Don’t count on that. It is possible. But if China were to embark on such a path, you must oppose it…And you must tell those Chinese that Zhou Enlai told you to do it.”
The book highlights significant events that caused Chinese leaders to reevaluate their policy focus. The first was a trifecta of events from 1989 to 1991, The Tiananmen Square Massacre, overseen by Deng and widely criticized by the United States and the West; The Gulf War to expel Iraq from Kuwait, which shocked China with the technical superiority of the Americans and the speed with which the war concluded; and the collapse of the Soviet Union. Following the collapse and the end of the cold war, China focused much more on the United States and after Tiananmen started to be more sensitive to human rights concerns of the liberal West even though these concerns dated at least as early as the Chinese annexation of Tibet. China also acquired a new respect for the military technical superiority of the US as demonstrated in the Gulf War.
When Deng Xiaoping became Premier, he followed the example of Singapore as a model of a democracy free capitalist economic system open to western investment and engagement under an authoritarian rule pioneered by Singapore prime minister Lee Kuan Yew.
The era from China opening to the United States and the West for investment and trade was given a central policy directive from Deng “Tao Guang Yang Hui” or “hide capabilities and bide time”, applying to political, economic, and military policy as directed by the CCP. During the US Kosovo war a Chinese military leader reiterated:
“what the PLA should do” in response to “the rise of military intervention” by the United States was to remember that “our approach is Tao Guang Yang Hui” He elaborated, “As a military, this means…vigorously developing ‘shashoujian’ equipment, [and following the principle of],’whatever the enemy is most afraid of, we develop that’.”
Second, at the political level, the trifecta and China’s strategic adjustment led Beijing to reverse its position on joining regional institutions. Memoirs of Chinese ambassadors are explicit on China’s need to join institutions to blunt American power in three ways: (1)stalling the institutions so they couldn’t become functional; (2) using them to constrain US freedom of maneuver; and (3) using them to reassure neighbors so they wouldn’t join a US-led balancing coalition…Even s, these efforts were taken consistent with Tau Guang Yang Hui’s principle of avoiding claims of leadership, which meant China refrained from launching new institutions; moreover, Deng himself had said that China’s diplomatic voice would grow loader once Tao Guang Yang Hui was retired.
Finally, the trifecta also shaped Chinese international economic policy…China raised new concerns in Beijing about its vulnerability to US leverage, and blunting these became the focus of Chinese efforts. China not only focused breaking economic sanctions, it also sought to secure MFN (most-favored-nation) status on a permanent basis, or permanent normal trading relations (PNTR). The goal was not to limit China’s dependence on the United States but to reduce the discretionary exercise of US economic power…It also pushed for WTO membership, hoping it would further tie Washington’s hands.
China limited its military expansion during this time to the development of mines, missiles, and conventional silent submarines. Their largest fleet in the world of silent submarines could surface right next to a US aircraft carrier without detection. In 1973, 75 year old Zhou Enlie was suffering from bladder cancer which Mao had ordered Zhou’s doctors to not reveal or treat, when he lamented that China had not yet acquired an aircraft carrier.
In 1992, after the Soviet Union collapse, a PLA delegation visited a new Soviet carrier, the Varyag, then under final construction in Ukraine on the Black Sea. China chose not to acquire it. Then five years later China’s top leaders changed their minds and launched a plan to acquire the Varyag that is worthy of a movie.
Xu Zengping joined the PLA in 1971 and left in 1980 to found a trading company that he claimed made him wealthy. Xu’s wife was a basketball player on China’s national team that played alongside Yao Ming’s mother. PLAN Vice Admiral He Pengfei recruited Xu to serve as the military’s intermediary in the Varyag purchase.
Consistent with Tao Guang Yang Hui, Xu knew he needed to deceive the world about his wealth, intentions, and government connections. Xu created the persona of an outlandish tycoon who wanted to use the carrier as a floating casino in Macao. Xu set up a shell company and spent $1 million to acquire licenses to operate the casino in Macao. Xu then bought one of the most expensive villas in Hong Kong for $30 million.
In October 1997, Xu went to Kiev to negotiate with the Ukrainian owners of the Varyag. The private owners acquired the Varyag during the massive neoliberal privatization of Soviet public assets after the collapse in 1991. After months of parties and millions in bribes, the owners finally agreed to sell the Varyag to Xu for $20 million. But Xu also needed the blueprints and the engines which were beyond Chinese capabilities to build at the time. The engines had already been installed but Xu got fake documents showing that the engines had been removed. Xu received 45 tons of blueprints and documents and the engines and then set out on the arduous process of moving the ship to Dalian China.
In all the government of China spend $120 million and in March 2002, the Varyag arrived in Dalian where it was rust protected and left in December 2005. Even the original Soviet name and markings were left on the carrier.
<> <> <> <> <> 
<> <> <> <> <> China’s First Carrier Liaoning
Then, in response to the Global Financial Crisis of 2008, which Chinese leaders took as a clear indication of the weakening of the US and the West, Chinese foreign policy entered a new more aggressive direction. The top level decision to build a carrier fleet was made in 2009. The Varyag was completed, renamed Liaoning , and commissioned on 25 September 2012.
After the 2008 Global Financial Crisis, China began to emphasize building regional order. It no longer felt the need to constrain itself fowir fear of rattling Washington or the wider region. The capabilities that carriers were know for were now fully in line with China’s own strategic objectives, which leaned increasingly toward enforcing maritime sovereignty and cultivating the ability to intervene regionally. And so, China entered the ranks of carrier-fielding great powers.
…the 2008 Global Financial Crisis caused a much bigger shift. China’s assessment of the relative power gap with the United States fell significantly and President Hu then officially revised Tao Guang Yang Hu by stressing “Actively Accomplishing Something” in his 2009 address.
In 2012 Wang Jisi, dean of Peking University’s School of International Relations wrote:
“Unlike East Asia, there is no U.S. led regional military alliance among the countries to the west, and there is no possibility that one will arise”…Instead, China had abondant resources and a continental vacuum in that direction, as well as the surplus capacity and dollar reserves to fill it with pipelines, railways, highways, and even overland Internet infrastructure that would reduce China’s dependence on the sea and bind the region tighter to China.
In 2013 Xi would launch the Belt and Road Initiative (BRI)
Mao’s Cultural Revolution began in 1966 and ended with Mao’s death in 1976. It impacted virtually all Chinese leaders from Deng to the present. Two stories of auto-didactic education are featured in this book:
<> <> <> <> <> 
<> <> <> <> <> The Silver Fox Wang Yi
On March 16, 2013, Chinese diplomat Wang Yi was formally promoted to minister of foreign affairs. The urbane but fierce defender of Chinese interests was sometimes known as a “silver fox” for both his “looks and his diplomatic wiles.” but he was also brilliant and diligent. After graduating high school during the Cultureal Revolution, Wang Li was sent to labor on a farm in northeast China for eight long years. A former classmate of his recalls that Want Li “did not waste his time” but engrossed himself in literature and history entirely on his own direction. When the Cultural Revolution ended , Wang Li’s diligence paid off, and he earned a spot at Bejing International Studies University, where he dedicated himself to Japanese language studies.
Wang Li married the daughter of Quian Jaidong an underling of Zhou Enlai and member of China’s first overseas delegations to the Geneva conference in the 1950s. Quian Jaidong became China’s UN ambassador in 1980.
<> <> <> <> <> 
<> <> <> <> <> Lin Liqun
On January 16,2016, The Asian Infrastructure Investment Bank (AIIB) was declared “open for business” and a grey haired enthusiast for English literature, Jin Liqun was elected its first president…Jin grew up in an educated but poor family with what was then an unusual passion for English literature. When he was sent to labor in the countryside for a decade during the Cultural Revolution, he spend three quarters of his meager annual salary and what little time he had after a day’s work in the fields continuing that pursuit. “I was outfitted with a worn out Remington typewriter and a copy of Webster”, he said later, as well as a radio he kept tuned to the BBC that gave his English a trace of the “standard BBC accent of the 1970s.” When the Cultural Revolution abated, the twenty nine year old autodidact won a seat at the Beijing Institute of Foreign Languages, excelled in graduate work, and was offered a faculty position…It was not to be. That same year, China joined the World Bank, and English speakers were needed to staff its new office in Washington…He spent a dozen years at the World Bank and then the Asian Development Bank, rising to become its first Chinese vice president, and developed a resume and Rolodex in multilateral finance no other Chinese official could match. When China decided to build its own development bank, Jin was the logical choice.
Another remarkable story about a misfit coming out the Cultural Revolution was previously blogged.
<> <> <> <> <> 
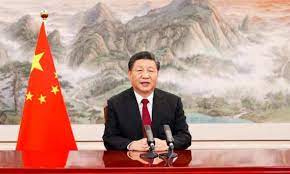
<> <> <> <> <> Xi Jinping
On October 18. 2017, General Secetary Xi Jinping, in a 3 1/2 hour 30,000 word speech announced the next great change in Chinese foreign policy.
The speech announced a “new era”, put forward timetables for China’s rejuvenation in 2049, promised greater Chinese activism in global governance, called for a “world-class” military, committed China to becoming a “global leader in innovation,” and declared that China would “become a leading country in comprehensive national strength and international influence.”
Like other changes in China’s grand strategy, this shift toward greater global ambition was driven by what Beijing saw as the West’s irreversible decay and decline. In 2016…the United Kingdom voted to leave the European Union, and Donald Trump was elected president of the United States. From China’s perspective–which is highly sensitive to changes in perception of American power–these to events were shocking. The world’s most powerful democracies were withdrawing from the international order they had helped erect, creating what China’s leadership and foreign policy elite has called a “period of historic opportunity” to expand the country’s strategic focus from Asia to the wider globe and its governance systems.